We asked Viston to modernize our fraud detection and AML monitoring with explainable AI and graph analytics while meeting regulator expectations.
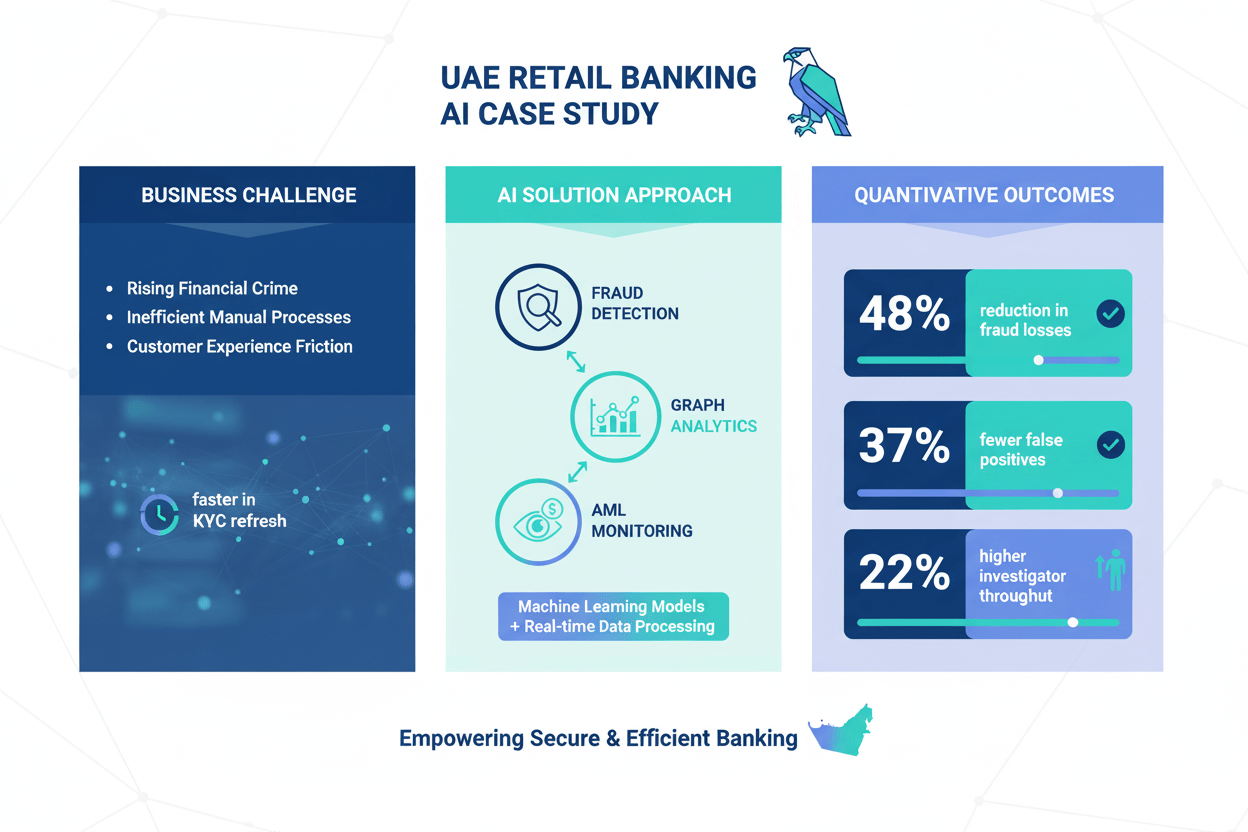
Business challenge
- High false positives in card fraud, rising mule activity, and manual KYC refresh.
- Fragmented rule engines and limited case investigation tooling.
Our approach and solution
- Built a streaming fraud scoring pipeline with graph features and explainable models.
- Upgraded AML monitoring with entity resolution and risk scoring; automated KYC refresh.
AI applications and benefits delivered
- Real-time fraud scoring with LightGBM and graph-derived features.
- Neo4j-based network risk scores to surface mule rings.
- SHAP-based explanations integrated into case management.
- LLM assistant for investigator summarization and SAR drafting with strict guardrails.
Cost of implementation
- USD 1,75,000 including data platform uplift and model validation.
Time to implement
- 7 months to full production across cards and retail payments.
Tools and technologies used
- Azure Databricks, Spark Structured Streaming, Kafka, Snowflake, Neo4j, LightGBM, SHAP, Elastic Stack, AKS, Key Vault, MLflow, Great Expectations, Power BI.
Quantitative outcomes
- 48% reduction in fraud losses on targeted products.
- 37% reduction in false positives.
- 60% faster KYC refresh turnaround.
- 22% higher investigator throughput.
Key performance indicators (KPIs) tracked
- Fraud loss rate bps, false positive rate, precision/recall, time-to-detect, AML alert productivity, SAR timeliness, model drift.
Pre- and post-implementation metrics
- Fraud loss rate: 7.8 bps → 4.1 bps.
- False positive rate: 92% → 58%.
- Average KYC TAT: 10 days → 4 days.
- Alerts per investigator per day: 18 → 22.
Stakeholder quotes or testimonials
- “Explainability made model sign-off straightforward with internal audit and the regulator.” — Head of Financial Crime.
- “Graph features exposed mule networks we couldn’t see with rules only.” — Fraud Strategy Lead.
Regulatory or compliance considerations
- UAE Central Bank AML/CFT guidance, FATF-aligned controls, PCI DSS scope containment, model risk policy adherence, challenger model testing, comprehensive audit logs, privacy-by-design.